Security and Privacy are two vitally important components of any successful society. Today’s connected world, where we carry computers in our pockets and share all our details on social networks, makes them even more so.
This section of Pocketnow is devoted to why security and privacy are important, how you can protect yourself in today’s connected world, and pitfalls to be aware of and avoid — with the objective of helping you and your loved ones stay safe in an ever-changing world.
~
So far in this series, we’ve talked about encrypting your Internet traffic using a VPN, how to avoid getting infected by malware, how to physically secure your phone, how to encrypt your communications, and more. To review our definitions, Privacy is the state or condition of being free from being observed by other people, and Security is the state of being free from danger or threat (which is the literal application of Privacy).
Unfortunately, one of the biggest “features” of our mobile devices is also one of the largest areas of concern when it comes to privacy: location tracking.
Location Tracking
Ten years ago, if I’d have told you that your service provider (T-Mobile, Verizon, Virgin, Xfinity, etc.), your ecosystem provider (Apple, Microsoft, Google, Samsung, etc.), and even websites you visit could know where you are, you would probably have argued they couldn’t or simply dismissed my claims out of hand. Even then, however, carriers could tell where you were to a startling degree of accuracy, and even websites could identify roughly where you were based only on your IP address.

Today, GPS, aGPS, and GLOSNASS can pinpoint your location down to a few feet – and nobody bats an eye. We use these “location services” for navigation, car services (like Lyft and Uber), to find restaurants and entertainment nearby, and even to track family members. The pictures we snap are tagged with the date, time, and location of where they were taken. Facebook and other social networks tell us when a “friend” is nearby. Again, we aren’t concerned because all these features are “convenient”.
Don’t believe me? Check out Google’s Timeline to see what location data one such company is collecting about you.
We’re trading our privacy for convenience.
GPS Not Required
The argument I’m often met with is that this location data is “private” – it’s not accessible to the public. That’s simply not true. Take a look at your “friends” on Facebook, for example. How many of them are actually your friends? How many of them are you comfortable with knowing where you are? How many are you comfortable with knowing who your children are, where they are, and what their schedules are? If you said you’re comfortable with all of them knowing, you’re more trustworthy than I am.

That notwithstanding, how many of those friends are using secure passwords? How many are using passwords unique to each site they log into (versus the same password for virtually every site they log into)? How many use 2-factor authentication? You’re not sure? All it takes is one of your friends’ accounts to be hacked or compromised and your pictures, your status updates, and your kids’ schedules are now accessible to a complete stranger. You can deny this happens, but every week we’re hearing about another hack and are being told to reset our passwords – and that’s just the intrusions that are reported by the media, how many go unreported, or even unnoticed?
The response I typically get to pointing out that inconvenient reality is that they can simply “turn their GPS off”. That’s nice – but there is a bigger problem, and it’s built into your cellphone and the way it works. You can’t “turn off” this vulnerability without taking the battery out of your phone or putting it in a bag that blocks electromagnetic waves.
Stingray
Even with WiFi and GPS/GLOSNASS turned off, your phone still “talks” to cell phone towers. It’s usually in communication with a few of them at any given time and, generally speaking, is connected to the one with the strongest signal. There is some overhead in hopping between towers, and a tower with a stronger signal may already be “full” and not able to take your phone’s connection, but the only way your phone can know that is by “talking” (albeit briefly, and without your knowledge) to any tower that it “hears”.
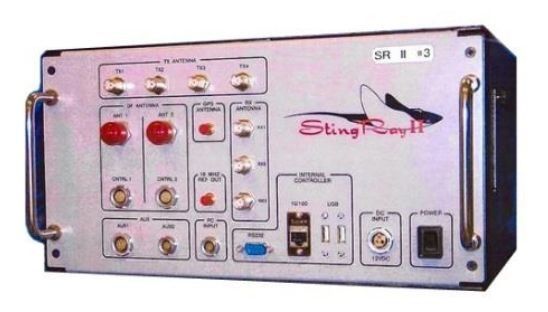
What if the cell phone tower that your phone is talking to isn’t really a cell phone tower? That’s exactly the case with the “Stingray”, a secret device used by various law enforcement and government agencies to spy on and track people – and most of the time (as court records have shown) without a warrant.
The way these devices work is by imitating a cell phone tower, devices then “see” them and try to connect with them, in so doing they disclose your phone’s unique identifier and the reported signal strength at which your phone “hears” the Stingray. With this information and some signal processing software, whoever is in control of these devices can identify and map the locations of every cellular device (phones, laptops, tablets, and now even smart watches and connected cars). The argument I hear most often about these is “if you have nothing to hide, you have nothing to fear”. But how many of these devices exist? Are all of them accounted for, or are a number of them “missing”? Are they always used only when authorized by a judge with a lawful warrant justifying their use? Is the information of all the other devices “seen” by these “spy boxes” discarded immediately, or is that data held on to for some undetermined time? The government won’t answer these questions – that alone should concern you.
Even if you’re comfortable with their use by law enforcement when supported by a sufficient warrant, are you comfortable with anyone in general having access to such hardware – because if even one such device is “in the wild” or “lost”, you can rest assured that it’s being duplicated and other such devices are being sold to whoever wants to buy them.
What Can You Do?
This is one of those articles where there really isn’t much that you, as an individual, can do. Yes, you can turn off location services or tell your photos app not to tag the location where your pictures are taken, but just by having your phone on, cellular providers and those with access to Stingray-type devices can know where you are.

What about inadvertently sharing private information with “friends” who are at an increased risk for having their accounts compromised (due to weak passwords, old passwords, failure to use 2-factor authentication, etc.)? To address those concerns I’m calling upon social network providers to add those as privacy options. For example, I should be able to choose to share my posts with friends and friends of friends, but only those who (a) are using “strong passwords”, and (b) have 2-factor authentication turned on and configured. Then, when “friends” would have seen one of my posts in their timeline, I’d like a big, red “NO” sign displayed alongside a message that says “Your friend has limited their posts to be seen by friends with secure accounts, and yours isn’t secure enough for them. Click here to change your password to a stronger one and to add 2-factor authentication to your account so you can see your friend’s posts”.
In the meantime, if you’re not using two-factor (or two-step) authentication on your accounts, go set it up. Google Authenticator is a pretty good app which works on Apple as well as Android devices and has support for several of the sites which I use.
I realize that this article, unlike the others so far, doesn’t include a lot of “here’s the problem, here’s the solution” scenarios. In this case, the best “solution” I can offer is the knowledge that the problems exist – and can fairly easily be exploited. Now it’s up to you to harden your accounts and put pressure on service providers, friends, and even family to do the same.

