As I write this review, my Facebook wall sits abuzz with consternation from friends and family alike, all of them complaining about the same offense in a rare show of unified ire. Facebook’s recent mandate that mobile users install its Messenger app, with all its Orwellian security permissions, has reignited a discussion more and more common among the general public: in today’s world, how much privacy are we really giving away … and how do we get some of it back?
To answer the latter question, cyber-security outfit Silent Circle came together with hardware firm Geeksphone to produce the Blackphone BP1 – a modern smartphone designed to “put privacy back in your hands.” The device uses a custom build of Android and a special suite of applications to deliver the most security-minded mobile software we’ve ever encountered. For those who put a premium on privacy, the Blackphone offers a combination of options never before seen in the consumer space.
It’s the consumer experience we’re focusing on with this review. While we’ve got a lot of expertise under the Pocketnow roof, we’re not set up to do the kind of technical testing that Ars Technica performed in its own run-in with the device – which we recommend checking out if you want a look into the Blackphone’s back end. Rather, we’re more interested in finding out how well the device works for the layman, the private citizen that makes up half of Blackphone’s target customer base for the version-1 product. (Our two review devices were loaned to us by the fine folks at GSM Nation, whom you should visit if you want a BP1 of your own.)
Regarding Blackphone from this perspective, we’re left with two impressions: 1) there’s never been a smartphone that gives you as many privacy tools as this; and 2) first-generation products, no matter how specialized, will always feel like first-generation products. Join us below, as we explore the world of the secure smartphone in our Blackphone review!
Video Review · Specs & Hardware
Software · Camera · Performance · Pros/Cons
Pricing/Availability · Conclusion · Scored For Me
Blackphone Review Video
Specs & Hardware
It goes without saying that the Blackphone is not the device you buy if you want to stand out. This is one of the most nondescript handsets we’ve ever seen, with even less hardware personality than the BlackBerry Z10 it’s built partly to compete with. Besides a small logo above the aft-mounted speakerphone, there’s positively no adornment on the device’s 8.4mm-thick plastic casing, which is finished in (what else?) matte black.
In the hand, this is a pretty insubstantial handset. Even after popping in the removable 2000 mAh (7.4 Wh) battery, the Blackphone comes in at a featherweight 119g – good news for those who like to travel light, but combined with the ho-hum casing materials, it gives the device a somewhat hollow feeling that belies its tall ambitions. That’s compounded by the thin material of the battery door, which utters the occasional creak when pressing the phone to the ear. Feedback on the power/volume keys isn’t terrific, nor are the viewing angles on the 4.7″ IPS display (720p). There’s nothing that stands out as particularly bad here, but the Blackphone hardware is some of the most forgettable we’ve ever seen. Then again, maybe that’s the point: it adds to the spylike mystique of the whole package.
The device’s processing power comes from a quad-core NVIDIA Tegra 4i running at 2GHz and backed up by a single gigabyte of LPDDR3 RAM, with onboard storage maxing out at 16GB (about 12.8GB of which is user-accessible). There’s a MicroSD card slot for storage expansion and a Micro SIM slot for your mobile carrier of choice. The Blackphone supports GSM, HSPA, and LTE and comes in global (LTE Cat 3 bands 3/7/20) and North American (LTE Cat 3 bands 4/7/17) flavors, meaning you’ll probably have little trouble connecting to AT&T or T-Mobile US here in the States.
Software
The real star of the whole Blackphone concept is the software driving it, combined with the applications bundled in out of the box. The former is a custom-built fork of Android 4.4.2 called PrivatOS; the latter is a mix of native and third-party titles and subscriptions worth almost $900.
PrivatOS
Firing up the Blackphone for the first time, it’s easy to mistake it for some type of Nexus prototype. The interface is almost exactly the same as stock Android, right down to the helpful mini-tutorials for mundane tasks like organizing folders and handling notifications. Only the sharp-looking black-and-yellow color scheme and the total lack of Google apps and services tips you off that the Blackphone is something else entirely.
PrivatOS 1.0.2 achieves some of its added security simply by enabling or mandating security features that Android has offered for some time. You’re prompted to set up a PIN or password to lock your device immediately upon first power-on; the more fun (but less secure) unlock options such as facial recognition and pattern unlock are either absent or, in the parlance of PrivatOS, “disabled by administrator, encryption policy, or credential storage.” Blackphone also prompts you to encrypt the entire device on first power-up; this is the same encryption option offered by most Android phones, but the software is much more insistent here than on other devices. That’s a good thing, since encrypting your smartphone is one of the single best ways to keep your mobile data secure.
Our favorite privacy feature baked into the Blackphone OS will be of particular interest to all those Facebook Messenger worriers mentioned in the introduction above. Following the path blazed by Android Jelly Bean and a few custom builds of Cyanogenmod, PrivatOS offers very granular control over how much access third-party apps have to your phone’s software. Upon downloading a third-party title (we prefer the Amazon appstore for this purpose, available here), you’re given the ability to choose exactly which bits of your phone a certain app gets access to. If, for example, you see no reason why a messaging client should be able to access your camera, you can restrict that particular permission while leaving the rest of the app’s functionality intact. And Blackphone’s default settings are, of course, rigorously pro-privacy: when we installed a barcode scanner with the default security parameters, the app wouldn’t function at all because PrivatOS had restricted the app’s camera permissions. Fortunately, it only took a short visit to the Security Center to enable that access so we could scan a QR code – and if we’d wanted to, we could have rescinded that permission again as soon as we were through with our scan.
Silent Circle Suite
Lying atop the baked-in security measures is a suite of apps that, when paired with included service memberships, take this device to the next level of secure communications. Whereas the PrivatOS’s baked-in functionality will still look and feel very familiar to an Android user, firing up any of the Silent Circle apps propels you into a world more befitting a device that calls itself “Blackphone.”
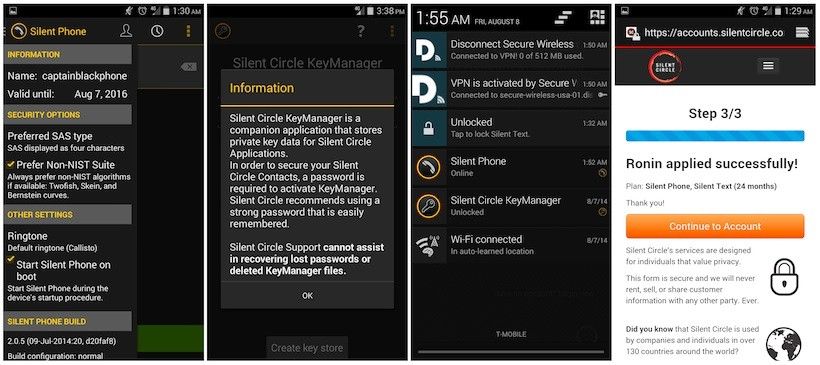
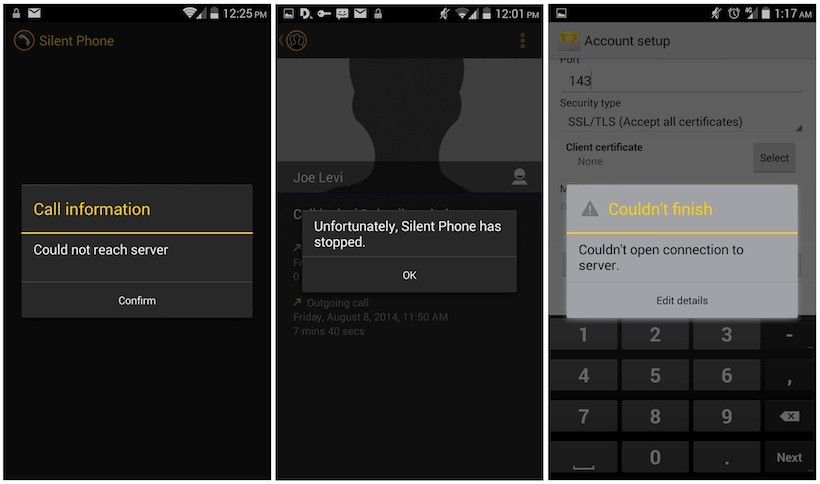
For phone calls too sensitive to go out over the cellular network, Silent Phone stands ready to push your voice through a secure SIP connection. This is a data-based VOIP call that uses ZRTP encryption to ensure that calls to and from other Blackphones (or other Android phones running the Silent Circle app) remain secure, while calls to “non-secure” lines through the Plain-Old Telephone System (POTS) arrive with at least some of their source information masked. For an added level of security –not to mention a degree of badassery– Silent Phone also generates one-time passphrases for use as a manual authentication. You’ll never feel more like a hardcore espionage agent than the first time you start a call to a Blackphone-toting friend with the challenge, “Salt Lake from Boston, secure; authenticate Yankee Foxtrot, over.”
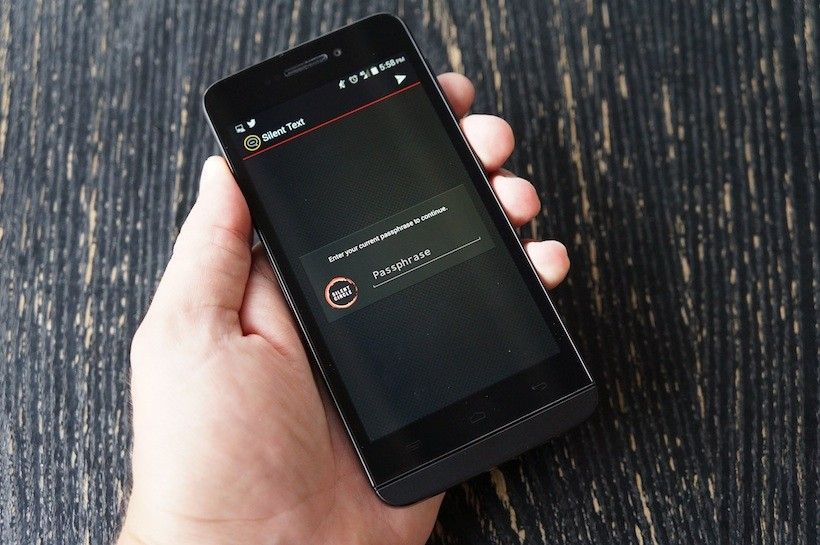
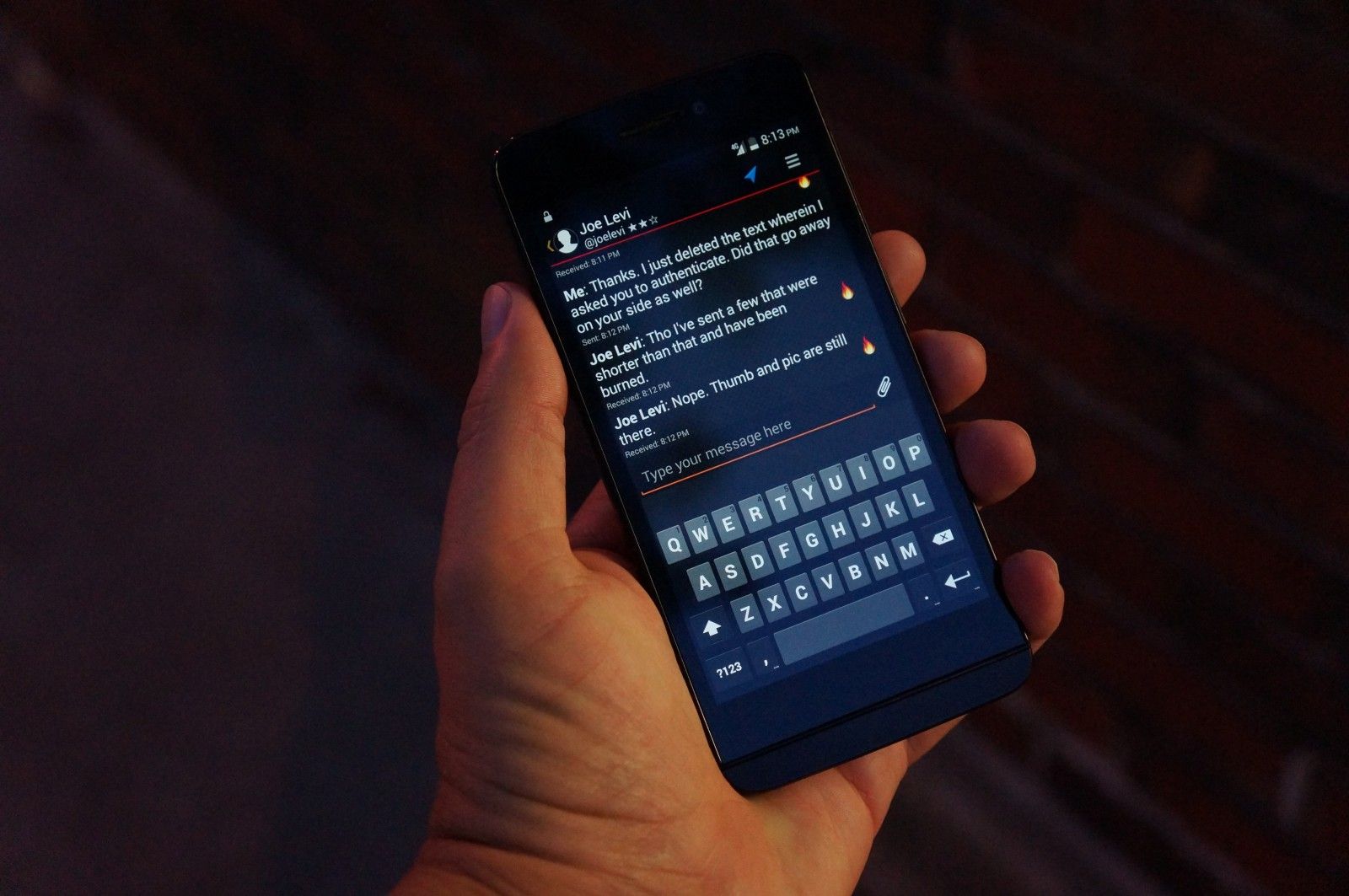
The security doesn’t let up over in the Silent Text hub, which replaces regular SMS messages with an IM-like exchange built on the Jabber protocol. Again, this requires that the receiving party be a paid Silent Circle subscriber with a Blackphone or a compatible device, and again it offers a variety of security tools you can’t find on the conventional equivalent. Messages sent through Silent Text can be set to auto-destruct after a set period ranging from a minute to a day, or deleted manually (from both phones). The screenshot utility is disabled within the app, preventing your messages from being turned against you unless your recipient has a camera handy. The entire app is protected by a separate passphrase, and a persistent toggle lives in the notification shade whenever Silent Text is active, providing a shortcut to quickly lock the entire app if you’re worried about someone imminently nicking your phone.
Both services draw from a central phonebook called Silent Contacts, and all three sit behind the protection of the Silent Circle KeyManager, which holds passwords for the entire Silent suite and can be used to lock or unlock the combined trio all at once. That’s handy, because the Blackphone is so dominated by passwords, PINs, and pass phrases that it’s easy to grow weary of the constant verification challenges.
Other Security Apps and Measures
The above protections alone would be enough to put Blackphone above all others in the “most secure smartphone” contest, but the company didn’t stop there. Also preloaded are tools for protecting (and strategically destroying) sensitive data, including:
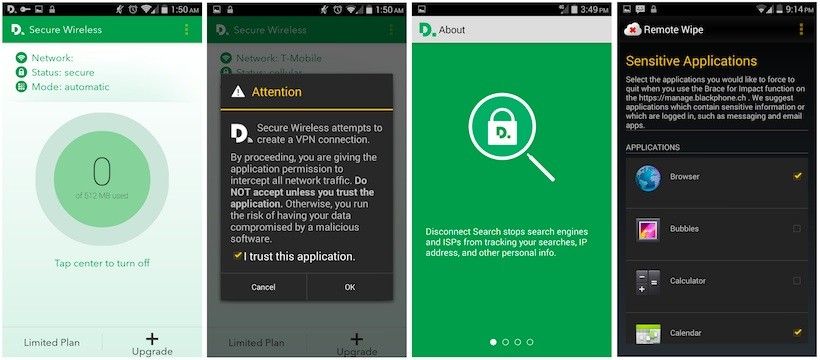
- Disconnect Secure Wireless. Provides the ability to encrypt and send all your traffic through a Virtual Private Network.
- SpiderOak BE. An encrypted cloud storage service with accompanying desktop software that uses “zero knowledge privacy” to ensure that not even the hosting servers ever have access to the plaintext data they’re passing.
- Remote Wipe. Allows you to remotely disable (force quit) applications via a web interface if your phone is lost or stolen, causing them to require a password before being restarted. Also provides for total erasure of the device if needed.
- Disconnect Search. Replaces the standard Google search bar on the homescreen with one from disconnect.me, a specialized VPN which serves as an anonymous front-end to Google, Yahoo, DuckDuckGo, and other search engines. This has the effect of masking your searches, IP addresses, and other personal information from search providers and websites which could otherwise log and retain such material for their own use.
Compromises and Vulnerabilities
Security often finds itself at odds with convenience, and with such an elaborate secrecy suite, Blackphone is no exception. The sheer number of passcodes alone will probably be enough to make some privacy proponents second-guess just how much protection they really need: just powering on the device requires passing through three security checkpoints (decrypt storage, PIN unlock, and Silent Circle KeyManager). And it doesn’t really get much easier from there.
The shortcomings don’t stop with pedestrian inconveniences like that, though; some of Blackphone’s biggest features fell short during our testing. Silent Phone offers outstanding vocal clarity when it’s working well, but in our experience (testing it on T-Mobile LTE and a high-speed office LAN) it more often than not suffers from drop-outs, high latency, and even total connection failures. During one particularly frustrating afternoon, the connectivity problems were so bad that Joe Levi and I couldn’t keep a call going even for 30 seconds, despite 90 minutes of trying. We also ran into issues sending media files via Silent Text, and with setting up a Google Apps account to sync properly with the device’s onboard email and calendar apps (which offer no additional security measures beyond the standard Android offerings). User error could well have played a part in that latter failure, but it’s a shame that implementing two-part authentication –a security measure we recommend for all Google Apps users– makes syncing with Blackphone so very difficult.
Finally, much has been made of the recent developments concerning how quickly Blackphone fell to root attempts at DefCon 2014, with a researcher able to obtain root access in less than 5 minutes. Blackphone, for its part, has been very forthcoming about the nature and extent of the issue, running a series of posts on its own blog where it makes the point that “in order to exploit any of the above-mentioned vulnerabilities the end-user would require physical access to the device and then perform the exploit.” How critical you consider this breach will depend on how much –and what sort of– security matters the most to you; it’s outside the scope of this review and mentioned only for the sake of thoroughness (and as an example of how quickly Blackphone’s builders can move to address an issue). Ars Technica has a solid write-up of the implications here.
For a more condensed list of Blackphone’s added security measures, see Joe Levi’s piece on the 10 ways Blackphone keeps you secure.
Camera
The Blackphone’s camera is an 8MP autofocus module with a dual-LED flash and a 5MP front-facing counterpart, backed up by the old Nexus-style camera viewfinder from Google. That’s the same software we bemoaned as unintuitive in our Nexus 5 review, and the switch to yellow accents from blue ones doesn’t mask the software’s unfriendliness.
The unpleasantness is magnified by the camera’s incredibly laggy performance, which often stretched startup time to four seconds or more – a pretty big deal when you’re in a hurry to catch that perfect moment. Shutter response and processing are also miserably slow, and the camera’s output is so average that we hesitate to recommend it to anyone serious about capturing good-looking photos or video.